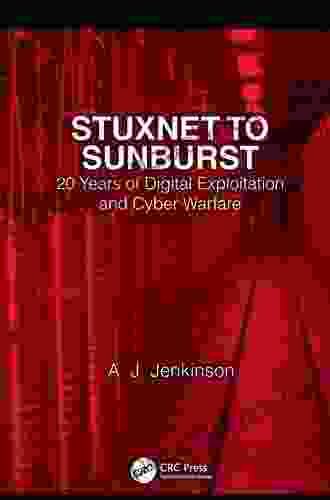
20 Years of Digital Exploitation and Cyber Warfare: Unmasking the Cybercriminal Landscape

In the rapidly evolving digital landscape, cyber threats have become an increasingly prevalent and sophisticated threat to businesses, governments, and individuals alike. "20 Years of Digital Exploitation and Cyber Warfare" is a groundbreaking book that delves into the murky depths of the cybercriminal underworld, exposing the tactics, motivations, and consequences of these malicious actors.
4.6 out of 5
| Language | : | English |
| File size | : | 4874 KB |
| Print length | : | 182 pages |
| Screen Reader | : | Supported |
A History of Cyber Exploits
The book traces the origins of digital exploitation back to the early days of the internet, where hackers and crackers engaged in playful mischief. However, as technology advanced, so did the sophistication and severity of cyberattacks. From the Morris worm of 1988 to the infamous Stuxnet virus of 2010, the book provides a comprehensive historical account of the most notable cyber exploits that have shaped the digital landscape.
Cyber Threats in the Modern Age
The book goes beyond historical accounts to examine the current state of cyber threats. It delves into the rise of ransomware, phishing scams, identity theft, and other sophisticated attacks that have become common in recent years. Readers will gain insights into the motivations of cybercriminals, including financial gain, espionage, activism, and personal grudges.
Unveiling the Cybercriminal Ecosystem
"20 Years of Digital Exploitation and Cyber Warfare" exposes the complex ecosystem of cybercriminals, ranging from lone wolves to organized crime syndicates. It explores the underground marketplaces where stolen data, malware, and hacking tools are traded. Readers will discover the hierarchy and specialization within the cybercriminal community, as well as the techniques they employ to evade detection and prosecution.
National Security and Cyber Warfare
Beyond individual and corporate victims, cyber threats have also emerged as a major national security concern. The book examines the role of nation-states in cyber espionage and warfare, analyzing the geopolitical implications and potential for escalation. It discusses the ethical and legal dilemmas surrounding the use of cyber weapons and the increasing need for international cooperation to combat cyber threats.
Countering Cyber Threats
"20 Years of Digital Exploitation and Cyber Warfare" not only provides a comprehensive overview of cyber threats but also offers practical advice on how to mitigate and respond to these attacks. It covers cybersecurity best practices, legal remedies for victims, and the role of law enforcement and intelligence agencies in combating cybercrime. Readers will gain valuable insights into how to protect their personal and corporate data from potential breaches.
"20 Years of Digital Exploitation and Cyber Warfare" is an essential read for anyone seeking a deeper understanding of the cybercriminal landscape. It provides a comprehensive historical account, analyzes current threats, and offers practical guidance on countering these attacks. By shedding light on the murky depths of the digital underworld, this book empowers readers to navigate the increasingly dangerous cyber frontier with confidence and resilience.
Call to Action
Secure your copy of "20 Years of Digital Exploitation and Cyber Warfare" today and equip yourself with the knowledge and tools to safeguard your digital assets and protect yourself from the ever-evolving cyber threats. Whether you are a business executive, a cybersecurity professional, or simply an informed citizen concerned about the implications of cyber warfare, this book is an invaluable resource that will empower you to navigate the digital landscape with confidence and resilience.
4.6 out of 5
| Language | : | English |
| File size | : | 4874 KB |
| Print length | : | 182 pages |
| Screen Reader | : | Supported |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Sarah Harding
Sarah Harding Voltaire
Voltaire David J Steward
David J Steward Julie M Creus
Julie M Creus Katherine E Knutson
Katherine E Knutson Jean Hanff Korelitz
Jean Hanff Korelitz Andrea Glaubacker
Andrea Glaubacker Andy Crouch
Andy Crouch Vladimir Nabokov
Vladimir Nabokov Charles Kegler
Charles Kegler Joshua L Cherniss
Joshua L Cherniss Jacqueline Pearce
Jacqueline Pearce Jerry A Mccoy
Jerry A Mccoy Andrew Machota
Andrew Machota Ms Rika
Ms Rika Peter Dicken
Peter Dicken Andrew Hammond
Andrew Hammond Haley Sweetland Edwards
Haley Sweetland Edwards Mary H Wagner
Mary H Wagner Franz Harper
Franz Harper
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Chris ColemanPractical Examples for Information Professionals: A Comprehensive Guide to...
Chris ColemanPractical Examples for Information Professionals: A Comprehensive Guide to...
 Jonathan FranzenUnleash the Enchanting Melodies of Frozen II: Music from the Motion Picture...
Jonathan FranzenUnleash the Enchanting Melodies of Frozen II: Music from the Motion Picture... Pablo NerudaFollow ·8.5k
Pablo NerudaFollow ·8.5k Ernest HemingwayFollow ·11.4k
Ernest HemingwayFollow ·11.4k J.R.R. TolkienFollow ·4k
J.R.R. TolkienFollow ·4k Hugo CoxFollow ·17.4k
Hugo CoxFollow ·17.4k Chadwick PowellFollow ·5.7k
Chadwick PowellFollow ·5.7k Bernard PowellFollow ·7.4k
Bernard PowellFollow ·7.4k Nathan ReedFollow ·14.2k
Nathan ReedFollow ·14.2k Danny SimmonsFollow ·12.1k
Danny SimmonsFollow ·12.1k
 Devin Ross
Devin RossUnlocking the Secrets of the Mind: Brain Mapping...
The human...
 Jacob Foster
Jacob FosterNovel of Misconception, Truth, and Love: A Journey of...
Unraveling the Lies We...
 Benji Powell
Benji PowellThe Only Technique You Will Ever Need: Unlocking the...
By [Author's...
 Pete Blair
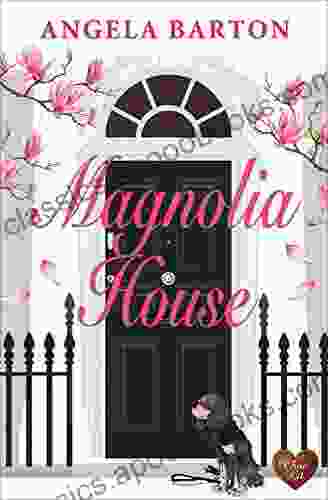
Pete BlairUnveiling the Enchanting World of 'Magnolia House' by...
A Literary...
4.6 out of 5
| Language | : | English |
| File size | : | 4874 KB |
| Print length | : | 182 pages |
| Screen Reader | : | Supported |